The OPW internship that I did between May and August 2014 offers sponsorship for attending a technical conference. I chose to go to FOSDEM which took place in Brussels, between 31 Jan and 1 March (Saturday and Sunday). It’s a free event for software developers and open source organizations to meet and share ideas. There are a ton of presentations on different topics you can attend: hardware, kernel, programming languages, distributed systems, web stuff, you name it. So, if you work or are interested into the IT industry, you’ll definitely find some interesting talks there.
The OPW internship that I did between May and August 2014 offers sponsorship for attending a technical conference. I chose to go to FOSDEM which took place in Brussels, between 31 Jan and 1 March (Saturday and Sunday). It’s a free event for software developers and open source organizations to meet and share ideas. There are a ton of presentations on different topics you can attend: hardware, kernel, programming languages, distributed systems, web stuff, you name it. So, if you work or are interested into the IT industry, you’ll definitely find some interesting talks there.
I arrived in Brussels two days before the conference because I wanted to have some time for visiting. I was lucky because the weather was perfect for visiting so I explored the city all day long. Brussels is famous especially for chocolate and beer, so I had to test them both to convince myself. :-).
On Saturday morning I arrived at the Universite Libre de Bruxelles where the conference was taking place. On their website you could download the schedule for a particular day. There, you could see all the main topics and each presentation was assigned to one large topic. All presentations belonging to the same topic were held in the same room. The schedule also had a map so you could know where to find a particular room in the campus.
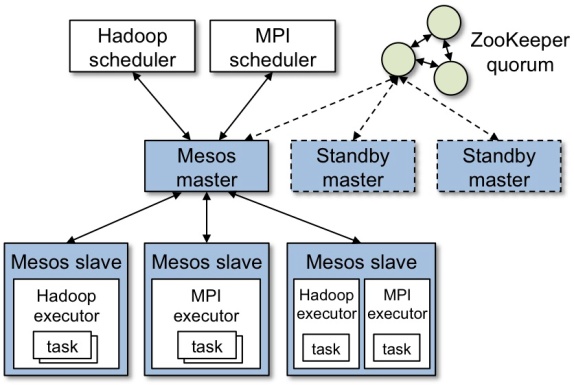
I’m currently interested in cloud computing and distributed systems so I got in the room where ‘Infrastructure as a service’ related presentations were held. The first presentation I attended was ‘Build distributed Fault-Tolerant systems with Apache Mesos’. Dave Lester, who presented was so impressed by the number of attenders that he took a picture with us and posted it on Twitter :-).My OPW internship was actually at Apache Mesos so I was very curious what the presentation would be about. At the beginning, it was an introduction into Apache Mesos, what is its purpose, how it achieves hardware abstraction for different kind of frameworks, what entities it’s composed of (master, slaves, scheduler, framework) and what are their purpose and also how the job scheduling process works. This was followed by a recorded demo, a sort of ‘Hello world’ applied to Apache Mesos, where a ‘print Hello FOSDEM’ command was ran on a set of machines. Basically one task was running over and over and Mesos was picking a machine (from a pool of machines) with free resource to run the command. In the end, Dave talked about Mesos at Twitter and how it improved the scalability especially during events like World Cup where the amount of traffic was increasing exponentially. He said that in 2010, before adopting Mesos and a more complex architecture, at each World Cup football match, when there was a goal or fault, the website was going down :-).
The next presentation I attended was called “GlusterFS -Overview & Future Directions”. I didn’t hear about GlusterFS before, but since it was held in that particular room, I assumed it was a distributed file system. Niels de Vos who is one of Gluster’s maintainers wanted to cover a few things throughout the presentation: give a short overview of the network file system, explain its components (servers, clients, storage bricks, volumes) and how they interconnect to form a scalable file system, talk about the current features, upcoming release and do a small demo about how to set up Gluster. Unfortunately he managed to cover just the first part because after 10 minutes of presentation, people started to ask questions over and over again. Basically Niels wasn’t able to continue its presentation because he answered all the questions. I find this a bit strange and it felt like he ran out of control with the talk. I can’t say whose fault was: the audience who should have left the presenter to continue the talk, or the presenter who maybe should have stopped the questions and answer them after the presentation was finished.
After that I attended two presentations related to OpenStack: “Cinder – the state of block storage in OpenStack” and “OpenStack and Xen”. Since OpenStack is very popular nowadays in the Cloud Computing area, I wanted to find out more about this subject. OpenStack is a very large and complex project used to obtain an IaaS platform. It has a lot of components each one with a different purpose: Nova (compute service), Glance (handles image service), Swift (object store), Keystone (does authentication), Horizon (the Web interface), Cinder (the block store). There are more of them but these are the basic infrastructure services.
On the first OpenStack presentation I found out some insights about Cinder component: how it achieves block storage (device level) abstraction and provides the user an API in order to use the resources (basically provides persistent storage to guest virtual machines), what are the main features (snapshot management, volume management) and some upcoming features.
The second OpenStack presentation was held by two guys: one that did the talking and one that actually made the presentation and the demo (this is what they said 🙂 ). First they presented some things about the Xen hypervisor, that it’s very secure and it’s used in the aviation and car industry because of that, and also the entire Amazon cloud is based on it. After the introduction came the integration of OpenStack on top of Xen. The component of OpenStack that is aware of the hypervisor underneath is Nova (the computing engine). Nova “talks” to Xen through an API driver called Libvirt which manages the VMs. After the overview there was a demo about how to deploy OpenStack on a Xen hypervisor: install your favorite Linux distro, install Xen (with apt-get install), reboot, clone the DevStack repo which offers a script that will install OpenStack, edit the script to specify Libvirt to use Xen, and run the script.
The second day I went to the ‘Security devroom’ where security presentations were being held. This is because the company I currently work for focuses on security products, and since the cloud stuff (my main interest) was covered in the first day, I thought that I should give security a try as well.
The first presentation I attended was “Web Security” by Habib Virji who is part of Samsung’s Open Source Group. The two topics were CSP (Content Security Policy) and Web Criptography. I found out about “Open Web Application Security Project (OWASP)”, an online community dedicated to web application security, which has a top ten list with web security threats. Two of them addressed in the presentation were “Cross-site Scripting (XSS)” and “Sensitive data exposure”. XSS can inject client side scripts in a web page. It can be prevented with CSP by allowing website owners to declare in a standard HTTP header, approved sources of content, that browsers should be allowed to load on that page. For the “Sensitive data exposure” issue the answer was “Web Cryptography API”, a JavaScript API capable of Hashing, Encryption/Decryption and Signature generation/verification.
The second presentation was “The Fuzzing Project” by Hanno Bock, who, to my surprise, is a freelance journalist from Berlin that contributes to open source in his free time J. Fuzzing is a testing technique that provides random data to the input of a program. This can lead to crashes or even discover security vulnerabilities that can allow an attacker to take over the system. “The Fuzzing Project” has some tutorials and file samples to help you get started with fuzzing and also a list of free software projects and how well they resist fuzzing attempts. I found out that many of the Linux tools I am using on a daily basis have security vulnerabilities, mostly because of bad memory management in C language. Being mostly a C coder, this made me more aware of security threats and how I should test the software I am developing.
The last presentation was “BIFUZ” and was held by two compatriots from Intel Romania J. BIFUZ stands for “Broadcast Intent FUZzing Framework for Android” and is an open source testing tool which can find Buffer Overflows, Java exceptions and other security vulnerabilities by fuzzing intents in Android applications. An “Intent” is a messaging object you can use to request an action from another app component. Bugs found can be easily reproduced and sent to Google for verification. Intel has recently entered the mobile phones and tablet markets with its Intel Atom processors and it seems BIFUZ was used to test its compatibility with Android OS.
To sum everything up, it was a nice experience for me, travel and open source worked magnificent together 🙂 . This conference motivated me to continue to work on open source projects and be part of open source communities.